The best useful Cisco CCNA Security 210-260 dumps exam questions and answers free download from leads4pass. Newest helpful Cisco CCNA Security 210-260 dumps pdf materials and vce youtube demo update free shared. “Implementing an Advanced Server Infrastructure” is the name of Cisco CCNA Security https://www.leads4pass.com/210-260.html exam dumps which covers all the knowledge points of the real Cisco exam. High quality Cisco CCNA Security 210-260 dumps pdf training resources and study guides download free try, pass Cisco 210-260 exam test easily at the first time.
Vendor: Cisco
Certifications: CCNA Security
Exam Name: Implementing Cisco Network Security
Exam Code: 210-260
Total Questions: 329 Q&As
Latest Cisco 210-260 dumps pdf materials free download: https://drive.google.com/open?id=0B_7qiYkH83VRcnI0SE83bHBvQ1k
Latest Cisco 210-060 dumps pdf materials free download: https://drive.google.com/open?id=0B_7qiYkH83VRSHJTTV9NMjQ0dmc
Cisco CCNA Security 210-260 Dumps Exam Real Questions And Answers (Q13-Q40)
QUESTION 13
Which two features are commonly used CoPP and CPPr to protect the control plane? (Choose two.)
A. QoS
B. traffic classification
C. access lists
D. policy maps
E. class maps
F. Cisco Express Forwarding
Correct Answer: AB
QUESTION 14
What is one requirement for locking a wired or wireless device from ISE?
A. The ISE agent must be installed on the device.
B. The device must be connected to the network when the lock command is executed.
C. The user must approve the locking action.
D. The organization must implement an acceptable use policy allowing device locking.
Correct Answer: A
QUESTION 15
Which three statements are characteristics of DHCP Spoofing? (choose three)
A. Arp Poisoning
B. Modify Traffic in transit
C. Used to perform man-in-the-middle attack
D. Physically modify the network gateway
E. Protect the identity of the attacker by masking the DHCP address
F. can access most network devices
Correct Answer: ABC
QUESTION 16
Which statement correctly describes the function of a private VLAN?
A. A private VLAN partitions the Layer 2 broadcast domain of a VLAN into subdomains
B. A private VLAN partitions the Layer 3 broadcast domain of a VLAN into subdomains
C. A private VLAN enables the creation of multiple VLANs using one broadcast domain
D. A private VLAN combines the Layer 2 broadcast domains of many VLANs into one major broadcast domain
Correct Answer: A
QUESTION 17
which feature allow from dynamic NAT pool to choose next IP address and not a port on a used IP address?
A. next IP
B. round robin
C. Dynamic rotation
D. Dynamic PAT rotation
Correct Answer: B
QUESTION 18
Which type of encryption technology has the broadcast platform support?
A. Middleware
B. Hardware
C. Software
D. File-level
Correct Answer: C
QUESTION 19
When an IPS detects an attack, which action can the IPS take to prevent the attack from spreading?
A. Deny the connection inline.
B. Perform a Layer 6 reset.
C. Deploy an antimalware system.
D. Enable bypass mode.
Correct Answer: A
QUESTION 20
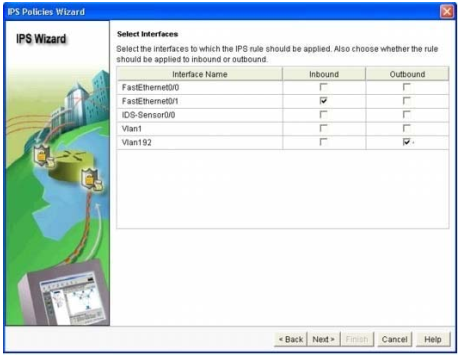
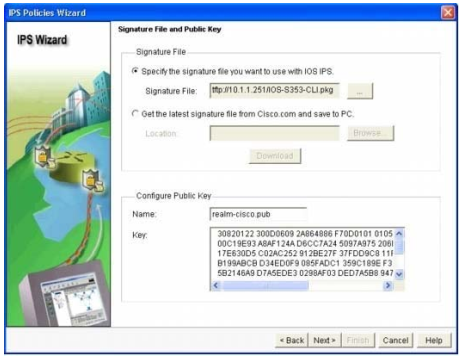
Which four tasks are required when you configure Cisco IOS IPS using the Cisco Configuration Professional IPS wizard? 210-260 dumps (Choose four.)
A. Select the interface(s) to apply the IPS rule.
B. Select the traffic flow direction that should be applied by the IPS rule.
C. Add or remove IPS alerts actions based on the risk rating.
D. Specify the signature file and the Cisco public key.
E. Select the IPS bypass mode (fail-open or fail-close).
F. Specify the configuration location and select the category of signatures to be applied to the selected interface(s).
Correct Answer: ABDF
Explanation:
Step 11. At the `Select Interfaces’ screen, select the interface and the direction that IOS IPS will be applied to, then click `Next’ to continue.
Step 12. At the `IPS Policies Wizard’ screen, in the `Signature File’ section, select the first radio button “Specify the signature file you want to use with IOS IPS”, then click the “…” button to bring up a dialog box to specify the location of the signature package file, which will be the directory specified in Step 6. In this example, we use tftp to download the signature package to the router.

Step 13. In the `Configure Public Key’ section, enter `realm-cisco.pub’ in the `Name’ text field, then copy and paste the following public key’s key-string in the `Key’ text field. This public key can be downloaded from Cisco.com.
QUESTION 21
Which ports need to be active for AAA server and a Microsoft server to permit Active Directory authentication?
A. 445 and 389
B. 888 and 3389
C. 636 and 4445
D. 363 and 983
Correct Answer: A
QUESTION 22
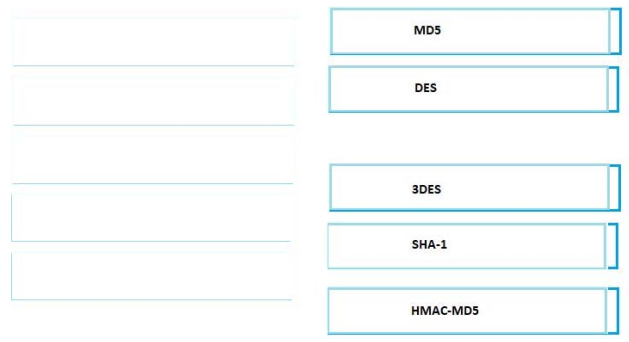
DRAG DROP
Drag the hash or algorithm from the left column to its appropriate category on the right.
Select and Place:
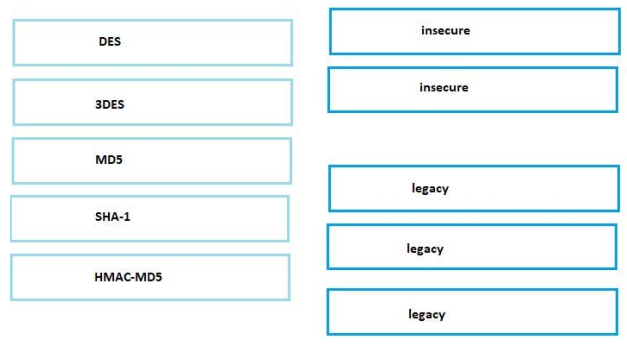
Correct Answer:
QUESTION 23
If a switch receives a superior BPDU and goes directly into a blocked state, what mechanism must be in use?
A. root guard
B. EtherChannel guard
C. loop guard
D. BPDU guard
Correct Answer: A
QUESTION 24
Which two are valid types of VLANs using PVLANs? 210-260 dumps (Choose two.)
A. Backup VLAN
B. Secondary VLAN
C. Promiscuous VLAN
D. Community VLAN
E. Isolated VLAN
Correct Answer: DE
QUESTION 25
Which two are the default settings for port security? (Choose two.)
A. Violation is Protect
B. Maximum number of MAC addresses is 1
C. Violation is Restrict
D. Violation is Shutdown
E. Maximum number of MAC addresses is 2
Correct Answer: BD
QUESTION 26
Refer to the exhibit.
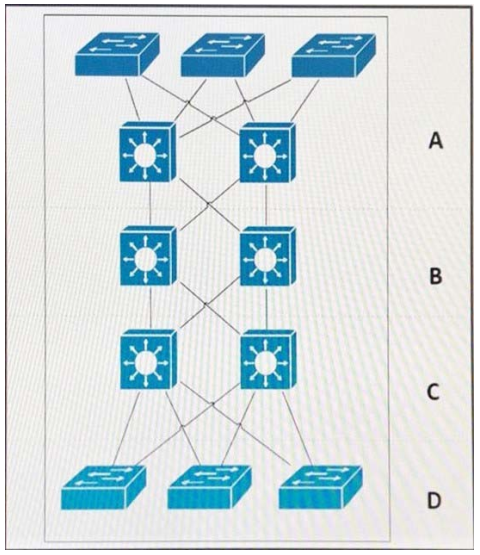
Which area represents the data center?
A. A
B. B
C. C
D. D
Correct Answer: A
QUESTION 27
Refer to the exhibit.
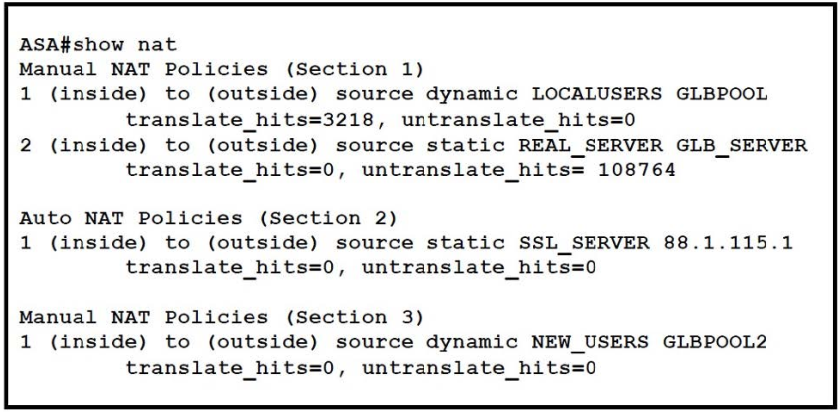
A network security administrator checks the ASA firewall NAT policy table with the show nat command.
Which statement is false?
A. First policy in the Section 1 is dynamic nat entry defined in the object configuration.
B. There are only reverse translation matches for the REAL_SERVER object.
C. NAT policy in Section 2 is a static entry defined in the object configuration.
D. Translation in Section 3 is used when a connection does not match any entries in first two sections.
Correct Answer: D
QUESTION 28
Which two are characteristics of RADIUS? (Choose two.)
A. Uses TCP ports 1812/1813
B. Uses UDP port 49
C. Encrypts only the password between user and server
D. Uses TCP port 49
E. Uses UDP ports 1812/1813
Correct Answer: CE
QUESTION 29
Which two types of firewalls work at layer 4 and above? (Choose two.)
A. Application level firewall
B. Circuit-level gateway
C. Static packet filter
D. Network Address Translation
E. Stateful inspection
Correct Answer: AB
QUESTION 30
When setting up a site-to-site VPN with PSK authentication on a Cisco router, which two elements must be configured under crypto map? (Choose two.)
A. nat
B. peer
C. pfs
D. reverse-route
E. transform-set
Correct Answer: BE
QUESTION 31
Which two commands are used to implement Resilient IOS Configuration? (Choose two.)
A. copy flash:/ios.bin tftp
B. copy running-config tftp
C. copy running-config startup-config
D. secure boot-image
E. secure boot-config
Correct Answer: DE
QUESTION 32
Which two events would cause the state table of a stateful firewall to be updated? 210-260 dumps (Choose two.)
A. when a connection’s timer has expired within the state table
B. when a connection is created
C. when rate-limiting is applied
D. when a packet is evaluated against the outbound access list and is denied
E. when an outbound packet is forwarded to the outbound interface
Correct Answer: AB
QUESTION 33
Which IPSec mode is used to encrypt traffic directly between a client and a server VPN endpoint?
A. transport mode
B. tunnel mode
C. aggressive mode
D. quick mode
Correct Answer: A
QUESTION 34
On an ASA, the policy that indicates that traffic should not be translated is often referred to as which of the following?
A. NAT zero
B. NAT forward
C. NAT null
D. NAT allow
Correct Answer: A
QUESTION 35
What is true of an ASA in transparent mode?
A. It requires a management IP address
B. It allows the use of dynamic NAT
C. It requires an IP address for each interface
D. It supports OSPF
Correct Answer: A
QUESTION 36
Which component offers a variety of security solutions, including firewall, IPS, VPN, antispyware, antivirus, and antiphishing features?
A. Cisco IOS router
B. Cisco ASA 5500-X Series Next Gen. Security appliance
C. Cisco 4200 series IPS appliance
D. Cisco ASA 5500 series security appliance
Correct Answer: B
QUESTION 37
How does a zone pair handle traffic if the policy definition of the zone pair is missing?
A. It permits all traffic without logging.
B. It drops all traffic.
C. It inspects all traffic.
D. It permits and logs all traffic.
Correct Answer: B
QUESTION 38
Which command do you enter to configure your firewall to conceal internal addresses?
A. no ip logging facility
B. no ip directed-broadcast
C. no ip inspect
D. no proxy-arp
E. no ip source-route
F. no ip inspect audit-trail
Correct Answer: D
QUESTION 39
Which IOS command do you enter to test authentication against a AAA server?
A. aaa authentication enable default test group tacacs+
B. dialer aaa suffix password C. ppp authentication chap pap test
D. test aaa-server authentication dialergroup username password Correct Answer: D
QUESTION 40
210-260 dumps Which technology can block a non-malicious program that is run from a local computer that has been disconnected from the network?
A. antivirus software
B. firewall
C. host IPS
D. network IPS
Correct Answer: C
The Following Are Some Reviews From Our Customers:
Why Lead 4 pass?
leads4pass is the best provider of IT learning materials and the right choice for you to pass Cisco CCNA Security 210-260 exam. Other brands started earlier, but the questions are not the newest and the price is relatively expensive. leads4pass provide the latest real and cheapest questions and answers, help you pass Cisco 210-260 exam easily at first try.

Get the newest Cisco CCNA Security 210-260 dumps exam practice files in PDF format free download from leads4pass. The best and most updated latest Cisco CCNA Security https://www.leads4pass.com/210-260.html dumps pdf training resources which are the best for clearing 210-260 test, and to get certified by Cisco CCNA Security, download one of the many PDF readers that are available for free. 100% success and guarantee to pass Cisco 210-260 exam.
High quality Cisco CCNA Security 210-260 dumps vce youtube:
https://youtu.be/seDmEyXcd3w