
Share EC-COUNCIL 312-50v11 exam questions and answers from leads4pass latest updated 312-50v11 dumps free of charge. Get the latest uploaded 312-50v11 dumps pdf from google driver online. To get the full EC-COUNCIL 312-50v11 dumps PDF or dumps VCE visit: https://www.leads4pass.com/312-50v11.html (Q&As: 429). all EC-COUNCIL 312-50v11 exam questions have been updated, the answer has been corrected!
Make sure your exam questions are real and effective to help you pass your first exam!
Table Of Content:
- EC-COUNCIL 312-50v11 Dumps Pdf
- EC-COUNCIL 312-50v11 Dumps Youtube
- EC-COUNCIL 312-50v11 Exam Questions
- EC-COUNCIL Discount Code 2021
[EC-COUNCIL 312-50v11 Dumps pdf] Latest EC-COUNCIL 312-50v11 Dumps PDF collected by leads4pass Google Drive:
https://drive.google.com/file/d/17-fQhaMT4pabFAeEFEFB3sEKYFQaMBnf/
Latest Update EC-COUNCIL 312-50v11 Exam Questions and Answers Online Test
QUESTION 1
Due to a slowdown of normal network operations, the IT department decided to monitor internet traffic for all of the
employees. From a legal standpoint, what would be troublesome to take this kind of measure?
A. All of the employees would stop normal work activities
B. IT department would be telling employees who the boss is
C. Not informing the employees that they are going to be monitored could be an invasion of privacy.
D. The network could still experience traffic slow down.
Correct Answer: C
QUESTION 2
What is the way to decide how a packet will move from an untrusted outside host to a protected inside that is behind a
firewall, which permits the hacker to determine which ports are open and if the packets can pass through the packetfiltering of the firewall?
A. Session hijacking
B. Firewalking
C. Man-in-the middle attack
D. Network sniffing
Correct Answer: B
QUESTION 3
You work for Acme Corporation as Sales Manager. The company has tight network security restrictions. You are trying
to steal data from the company\\’s Sales database (Sales.xls) and transfer them to your home computer. Your company
filters and monitors traffic that leaves from the internal network to the Internet. How will you achieve this without raising
suspicion?
A. Encrypt the Sales.xls using PGP and e-mail it to your personal gmail account
B. Package the Sales.xls using Trojan wrappers and telnet them back your home computer
C. You can conceal the Sales.xls database in another file like photo.jpg or other files and send it out in an innocent
looking email or file transfer using Steganography techniques
D. Change the extension of Sales.xls to sales.txt and upload them as attachment to your hotmail account
Correct Answer: C
QUESTION 4
Larry, a security professional in an organization, has noticed some abnormalities In the user accounts on a web server.
To thwart evolving attacks, he decided to harden the security of the web server by adopting a countermeasures to
secure the accounts on the web server.
Which of the following countermeasures must Larry implement to secure the user accounts on the web server?
A. Enable unused default user accounts created during the installation of an OS
B. Enable all non-interactive accounts that should exist but do not require interactive login
C. Limit the administrator or toot-level access to the minimum number of users
D. Retain all unused modules and application extensions
Correct Answer: C
QUESTION 5
To determine if a software program properly handles a wide range of invalid input, a form of automated testing can be
used to randomly generate invalid input in an attempt to crash the program.
What term is commonly used when referring to this type of testing?
A. Randomizing
B. Bounding
C. Mutating
D. Fuzzing
Correct Answer: D
QUESTION 6
Let\\’s imagine three companies (A, B and C), all competing in a challenging global environment. Company
A and B are working together in developing a product that will generate a major competitive advantage for
them. Company A has a secure DNS server while company B has a DNS server vulnerable to spoofing.
With a spoofing attack on the DNS server of company B, company C gains access to outgoing e-mails
from company B.
How do you prevent DNS spoofing?
A. Install DNS logger and track vulnerable packets
B. Disable DNS timeouts
C. Install DNS Anti-spoofing
D. Disable DNS Zone Transfer
Correct Answer: C
QUESTION 7
A newly joined employee. Janet, has been allocated an existing system used by a previous employee. Before issuing
the system to Janet, it was assessed by Martin, the administrator. Martin found that there were possibilities of
compromise through user directories, registries, and other system parameters. He also Identified vulnerabilities such as
native configuration tables, incorrect registry or file permissions, and software configuration errors. What is the type of
vulnerability assessment performed by Martin?
A. Credentialed assessment
B. Database assessment
C. Host-based assessment
D. Distributed assessment
Correct Answer: C
Explanation: The host-based vulnerability assessment (VA) resolution arose from the auditors\\’ got to periodically
review systems. Arising before the net becoming common, these tools typically take an “administrator\\’s eye” read of
the setting by evaluating all of the knowledge that an administrator has at his or her disposal. UsesHost VA tools verify
system configuration, user directories, file systems, registry settings, and all forms of other info on a number to gain
information about it. Then, it evaluates the chance of compromise. it should also live compliance to a predefined
company policy so as to satisfy an annual audit. With administrator access, the scans area unit less possible to disrupt
traditional operations since the computer code has the access it has to see into the complete configuration of the
system.
What it Measures Host VA tools will examine the native configuration tables and registries to spot not solely apparent
vulnerabilities, however additionally “dormant” vulnerabilities ?those weak or misconfigured systems and settings which
will be exploited when an initial entry into the setting. Host VA solutions will assess the safety settings of a user account
table; the access management lists related to sensitive files or data; and specific levels of trust applied to other systems.
The host VA resolution will a lot of accurately verify the extent of the danger by determinant however way any specific
exploit could also be ready to get.
QUESTION 8
What piece of hardware on a computer\\’s motherboard generates encryption keys and only releases a part of the key
so that decrypting a disk on a new piece of hardware is not possible?
A. CPU
B. GPU
C. UEFI
D. TPM
Correct Answer: D
QUESTION 9
what firewall evasion scanning technique make use of a zombie system that has low network activity as well as its
fragment identification numbers?
A. Decoy scanning
B. Packet fragmentation scanning
C. Spoof source address scanning
D. Idle scanning
Correct Answer: D
The idle scan could be a communications protocol port scan technique that consists of causing spoofed packets to a pc
to seek out out what services square measure obtainable. this can be accomplished by impersonating another pc whose
network traffic is extremely slow or nonexistent (that is, not transmission or receiving information). this might be
associate idle pc, known as a “zombie”. This action are often done through common code network utilities like nmap
and hping. The attack involves causing solid packets to a particular machine target in an attempt to seek out distinct
characteristics of another zombie machine. The attack is refined as a result of there\\’s no interaction between the
offender pc and also the target: the offender interacts solely with the “zombie” pc. This exploit functions with 2 functions,
as a port scanner and a clerk of sure informatics relationships between machines. The target system interacts with the
“zombie” pc and distinction in behavior are often discovered mistreatment totally different|completely different “zombies”
with proof of various privileges granted by the target to different computers. The overall intention behind the idle scan is
to “check the port standing whereas remaining utterly invisible to the targeted host.” The first step in execution associate
idle scan is to seek out associate applicable zombie. It must assign informatics ID packets incrementally on a worldwide
(rather than per-host it communicates with) basis. It ought to be idle (hence the scan name), as extraneous traffic can
raise its informatics ID sequence, confusing the scan logic. The lower the latency between the offender and also the
zombie, and between the zombie and also the target, the quicker the scan can proceed. Note that once a port is open,
IPIDs increment by a pair of. Following is that the sequence: offender to focus on -> SYN, target to zombie ->SYN/ACK,
Zombie to focus on -> RST (IPID increment by 1) currently offender tries to probe zombie for result. offender to Zombie
->SYN/ACK, Zombie to offender -> RST (IPID increment by 1) So, during this method IPID increments by a pair of
finally. When associate idle scan is tried, tools (for example nmap) tests the projected zombie and reports any issues
with it. If one does not work, attempt another. Enough net hosts square measure vulnerable that zombie candidates are
not exhausting to seek out. a standard approach is to easily execute a ping sweep of some network. selecting a network
close to your supply address, or close to the target, produces higher results. you\\’ll be able to attempt associate idle
scan mistreatment every obtainable host from the ping sweep results till you discover one that works. As usual, it\\’s
best to raise permission before mistreatment someone\\’s machines for surprising functions like idle scanning. Simple
network devices typically create nice zombies as a result of {they square measure|they\\’re} normally each underused
(idle) and designed with straightforward network stacks that are susceptible to informatics ID traffic detection. While
distinguishing an acceptable zombie takes some initial work, you\\’ll be able to keep re-using the nice ones. as an
alternative, there are some analysis on utilizing unplanned public internet services as zombie hosts to perform similar
idle scans. leverage the approach a number of these services perform departing connections upon user submissions
will function some quite poor\\’s man idle scanning.
QUESTION 10
Which of the following incident handling process phases is responsible for defining rules, collaborating human
workforce, creating a back-up plan, and testing the plans for an organization?
A. Preparation phase
B. Containment phase
C. Identification phase
D. Recovery phase
Correct Answer: A
QUESTION 11
Why containers are less secure that virtual machines?
A. Host OS on containers has a larger surface attack.
B. Containers may full fill disk space of the host.
C. A compromise container may cause a CPU starvation of the host.
D. Containers are attached to the same virtual network.
Correct Answer: A
QUESTION 12
Sam, a professional hacker. targeted an organization with intention of compromising AWS IAM credentials. He
attempted to lure one of the employees of the organization by initiating fake calls while posing as a legitimate employee.
Moreover, he sent phishing emails to steal the AWS 1AM credentials and further compromise the employee\\’s account.
What is the technique used by Sam to compromise the AWS IAM credentials?
A. Social engineering
B. insider threat
C. Password reuse
D. Reverse engineering
Correct Answer: A
QUESTION 13
In the field of cryptanalysis, what is meant by a “rubber-hose” attack?
A. Forcing the targeted keystream through a hardware-accelerated device such as an ASIC.
B. A backdoor placed into a cryptographic algorithm by its creator.
C. Extraction of cryptographic secrets through coercion or torture.
D. Attempting to decrypt ciphertext by making logical assumptions about the contents of the original plaintext.
Correct Answer: C
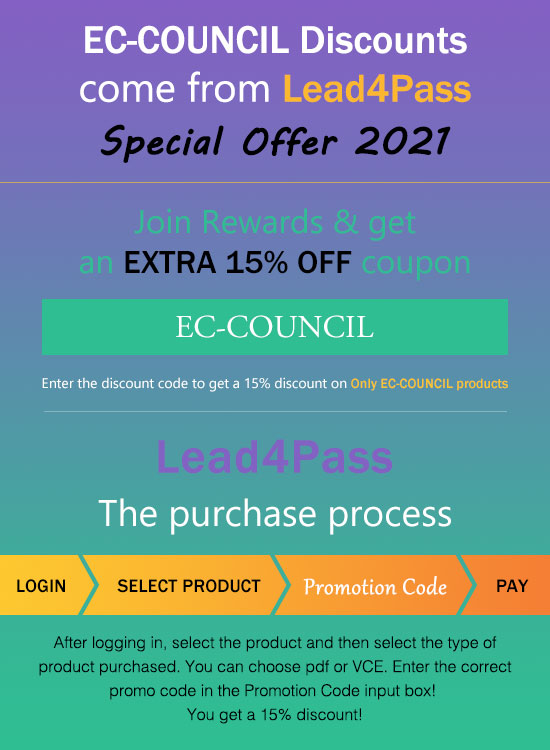
leads4pass EC-COUNCIL Discount Code 2021
The latest EC-COUNCIL exam discount code for 2021. leads4pass is valid throughout the year.
Select the purchased test questions and enter the discount code in the “Promotion Code:” input box to enjoy a 15% discount!
For the full EC-COUNCIL 312-50v11 exam dumps from leads4pass 312-50v11 Dumps pdf or Dumps VCE visit: https://www.leads4pass.com/312-50v11.html (Q&As: 429 dumps)
ps.
Get free EC-COUNCIL 312-50v11 dumps PDF online: https://drive.google.com/file/d/17-fQhaMT4pabFAeEFEFB3sEKYFQaMBnf/
![[2018 New Version] Best Choice to Pass Cisco CCNP Wireless 642-737 Dumps Exam Resources Youtube Demo (Q1-Q30)](https://www.latestvce.com/wp-content/themes/blogstream/img/thumb-medium.png)
