
Get free EC-COUNCIL ECSAV10 exam practice questions online can help you improve your exam success rate.
Free EC-COUNCIL ECSAV10 exam questions are part of leads4pass ECSAV10 Exam Dumps.
Get the complete ECSAV10 Exam Dumps https://www.leads4pass.com/ecsav10.html (Total Questions: 354 Q&A) helps you pass the exam 100% successfully. All exam questions and answers come from EC-COUNCIL exam experts. Guaranteed to be true and valid! All examination questions are updated throughout the year to ensure immediate validity.
The latest update EC-COUNCIL ECSAV10 PDF download online
Free EC-COUNCIL ECSAV10 exam PDF download online. All exam PDFs are part of the latest update from leads4pass EC-COUNCIL ECSAV10 PDF. Get the complete EC-COUNCIL ECSAV10 PDF at leads4pass
The latest updated EC-COUNCIL ECSAV10 exam practice questions online free practice
QUESTION #1
Which of the following roles of Microsoft Windows Active Directory refers to the ability of an active directory to transfer
roles to any domain controller (DC) in the enterprise?
A. Master Browser (MB)
B. Global Catalog (GC)
C. Flexible Single Master Operation (FSMO)
D. Rights Management Services (RMS)
Correct Answer: C
QUESTION #2
An attacker targeted to attack network switches of an organization to steal confidential information such as
network subscriber information, passwords, etc. He started transmitting data through one switch to another
by creating and sending two 802.1Q tags, one for the attacking switch and the other for victim switch. By
sending these frames. The attacker is fooling the victim switch into thinking that the frame is intended for it.
The target switch then forwards the frame to the victim port.
Identify the type of attack being performed by the attacker?
A. SNMP brute forcing
B. MAC flooding
C. IP spoofing
D. VLAN hopping
Correct Answer: D
QUESTION #3
George, an ex-employee of Netabb Ltd. with bruised feelings due to his layoff, tries to take revenge against the
company. He randomly tried several attacks against the organization. As some of the employees used weak passwords
to their user accounts, George was successful in cracking the user accounts of several employees with the help of a
common passwords file. What type of password cracking attack did George perform?
A. Hybrid attack
B. Dictionary attack
C. Brute forcing attack
D. Birthday attack
Correct Answer: B
QUESTION #4
Variables are used to define parameters for detection, specifically those of your local network and/or specific servers or
ports for inclusion or exclusion in rules. These are simple substitution variables set with the var keyword. Which one of
the following operators is used to define meta-variables?
A. “$”
B. “#”
C. “*”
D. “?”
Correct Answer: A
QUESTION #5
Identify the person who will lead the penetration-testing project and be the client’s point of contact.
A. Database Penetration Tester
B. Policy Penetration Tester
C. Chief Penetration Tester
D. Application Penetration Tester
Correct Answer: C
QUESTION #6
Sarah is a pentester at JK Hopes and Sons based in Las Vegas. As a part of the penetration testing, she
was asked to perform the test without exposing the test to anyone else in the organization. Only a few
people in the organization know about the test. This test covers the organization\’s security monitoring,
incident identification, and response procedures.
What kind of pen testing is Sarah performing?
A. Double-blind Testing
B. Announced Testing
C. Unannounced Testing
D. Blind Testing
Correct Answer: A
QUESTION #7
Michael, a penetration tester of Rolatac Pvt. Ltd., has completed his initial penetration testing, and now he needs to
create a penetration testing report for company\’s client, management, and top officials for their reference. For this, he
created a report providing a detailed summary of the complete penetration testing process of the project that he has
undergone, its outcomes, and recommendations for future testing and exploitation.
In the above scenario, which type of penetration testing report has Michael prepared?
A. Host report
B. Activity report
C. User report
D. Executive report
Correct Answer: D
QUESTION #8
In the TCP/IP model, the transport layer is responsible for the reliability and flow control from the source to the destination. TCP provides the mechanism for flow control by allowing the sending and receiving hosts to communicate. A flow control mechanism avoids the problem with a transmitting host overflowing the buffers in the receiving host.

A. Sliding Windows
B. Windowing
C. Positive Acknowledgment with Retransmission (PAR)
D. Synchronization
Correct Answer: C
QUESTION #9
Which of the following scan option is able to identify the SSL services?
A. -sS
B. -sV
C. -sU
D. -sT
Correct Answer: B
QUESTION #10
Linson, an employee in Skitac Ltd., notices a USB flash drive on the pavement of the company. Before he
could hand it over to the security guard, he tries to check it out. He connects it with an OTG to his mobile
phone and finds some of his favorite music playlists and games. He tries to download them into his mobile,
but very lately he came to know that he has been attacked and some of his sensitive financial information
was exposed to attackers.
What type of attacks did Linson face?
A. Social engineering attack
B. Phishing attack
C. Wardriving attack
D. Impersonation attack
Correct Answer: A
QUESTION #11
Rule of Engagement (ROE) is the formal permission to conduct a pen-test. It provides top-level guidance for conducting penetration testing. Various factors are considered while preparing the scope of ROE which clearly explain the limits associated with the security test.
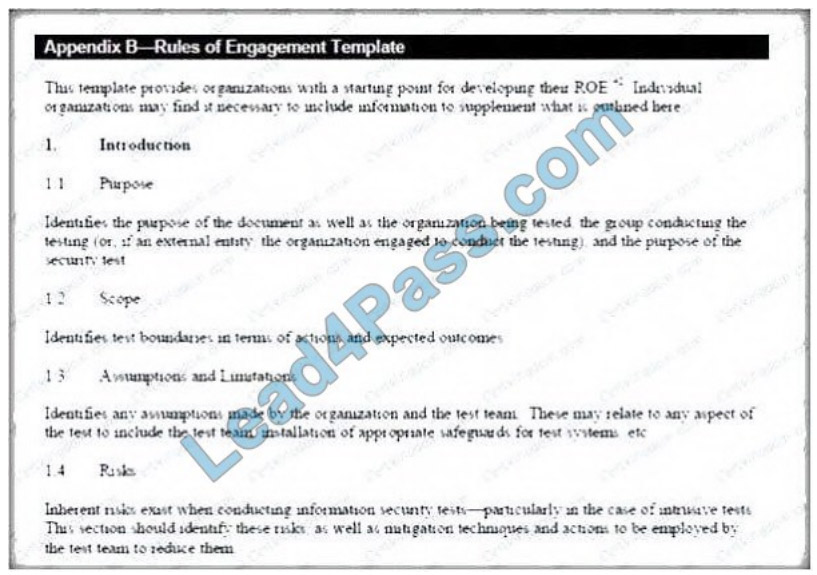
Which of the following factors is NOT considered while preparing the scope of the Rules of Engagement (ROE)?
A. A list of employees in the client organization
B. A list of acceptable testing techniques
C. Specific IP addresses/ranges to be tested
D. Points of contact for the penetration testing team
Correct Answer: A
QUESTION #12
During a DHCP handshake in an IPv4 network, which of the following messages contains the actual IP addressing
information for the clients to use?
A. DHCPDISCOVER
B. DHCPACK
C. REPLY
D. SOLICIT
Correct Answer: B
QUESTION #13
Sandra, a wireless network auditor, discovered her client is using WEP. To prove the point that the WEP
encryption is very weak, she wants to decrypt some WEP packets. She successfully captured the WEP
data packets, but could not reach the content as the data is encrypted.
Which of the following will help Sandra decrypt the data packets without knowing the key?
A. Fragmentation Attack
B. Chopchop Attack
C. ARP Poisoning Attack
D. Packet injection Attack
Correct Answer: B
leads4pass is updated throughout the year. EC-COUNCIL ECSAV10 exam dumps https://www.leads4pass.com/ecsav10.html (PDF + VCE).
Guaranteed immediate validity! All exam questions have been verified to ensure that they are true and valid!
ps.
Free EC-COUNCIL ECSAV10 exam PDF download online. All exam PDFs are part of the latest update from leads4pass EC-COUNCIL ECSAV10 PDF.
Get the complete EC-COUNCIL ECSAV10 PDF at leads4pass
![[JUNE 2021] Share the latest updated EC-COUNCIL 312-50V11 exam dumps from Leads4Pass with PDF and VCE](https://www.latestvce.com/wp-content/themes/blogstream/img/thumb-medium.png)
